Researches state Grindr has understood in regards to the safety flaw for a long time, but nonetheless has not fixed it
Grindr along with other homosexual dating apps continue steadily to expose the precise location of these users.
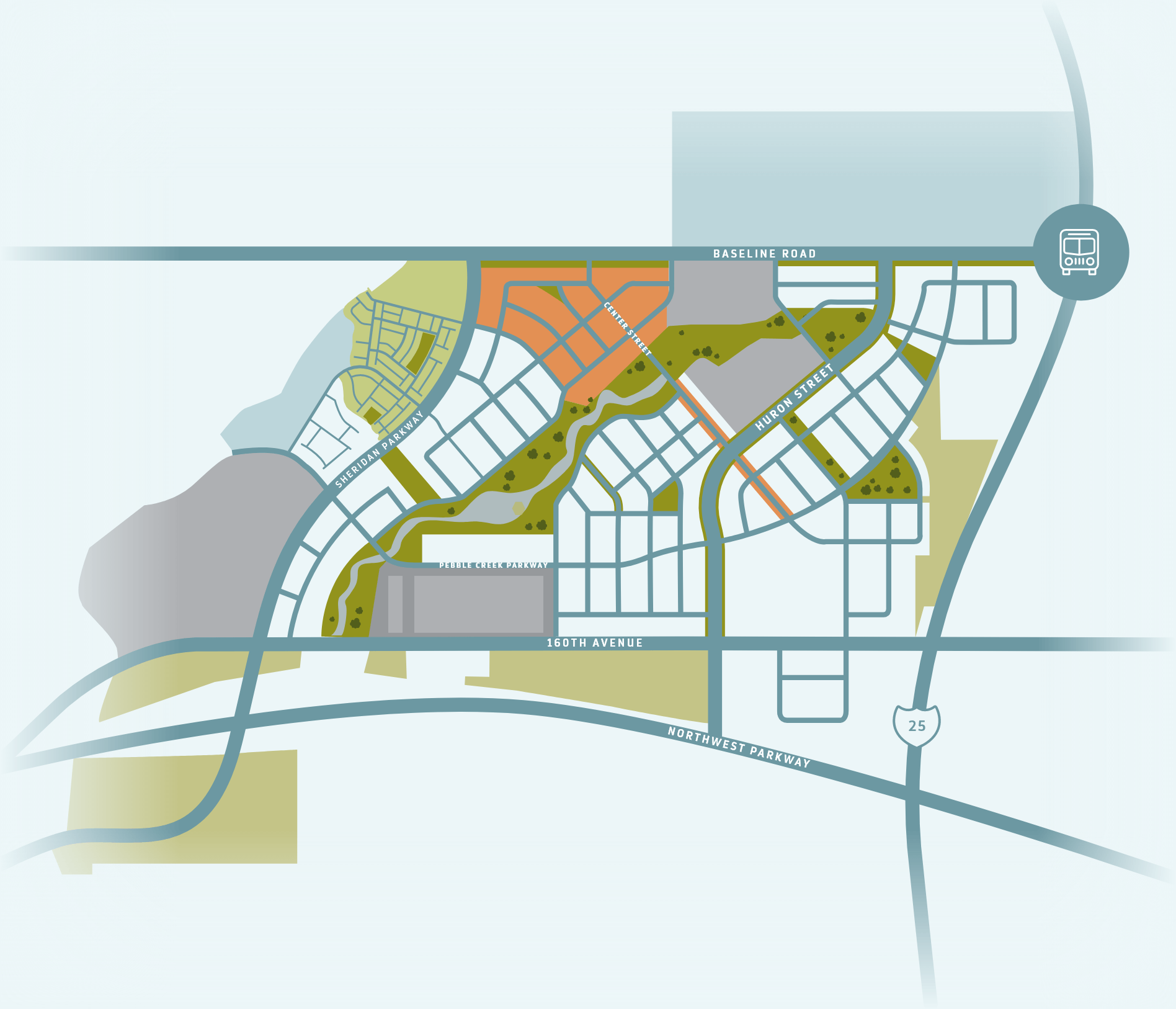
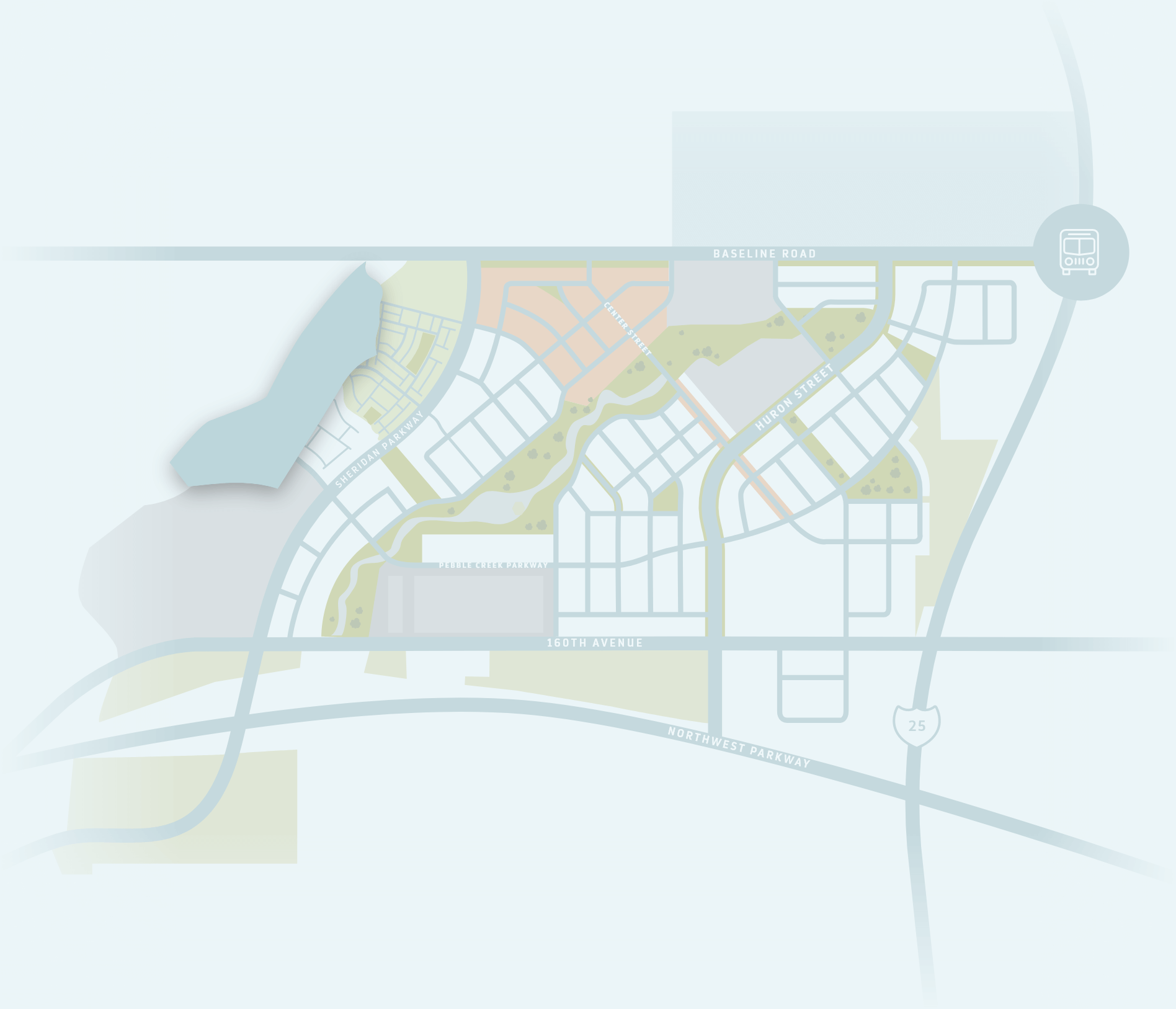
That’s relating to a report from BBC Information, after cyber-security researchers at Pen Test Partners could actually develop a map of application users over the city  of London — one which could show a user’s location that is specific.
of London — one which could show a user’s location that is specific.
What’s more, the scientists told BBC Information that the difficulty happens to be understood for years, but some for the biggest homosexual dating apps have yet to upgrade their pc software to repair it.
The scientists have actually evidently provided Grindr, Recon to their findings and Romeo, but stated just Recon has made the mandatory modifications to correct the problem.
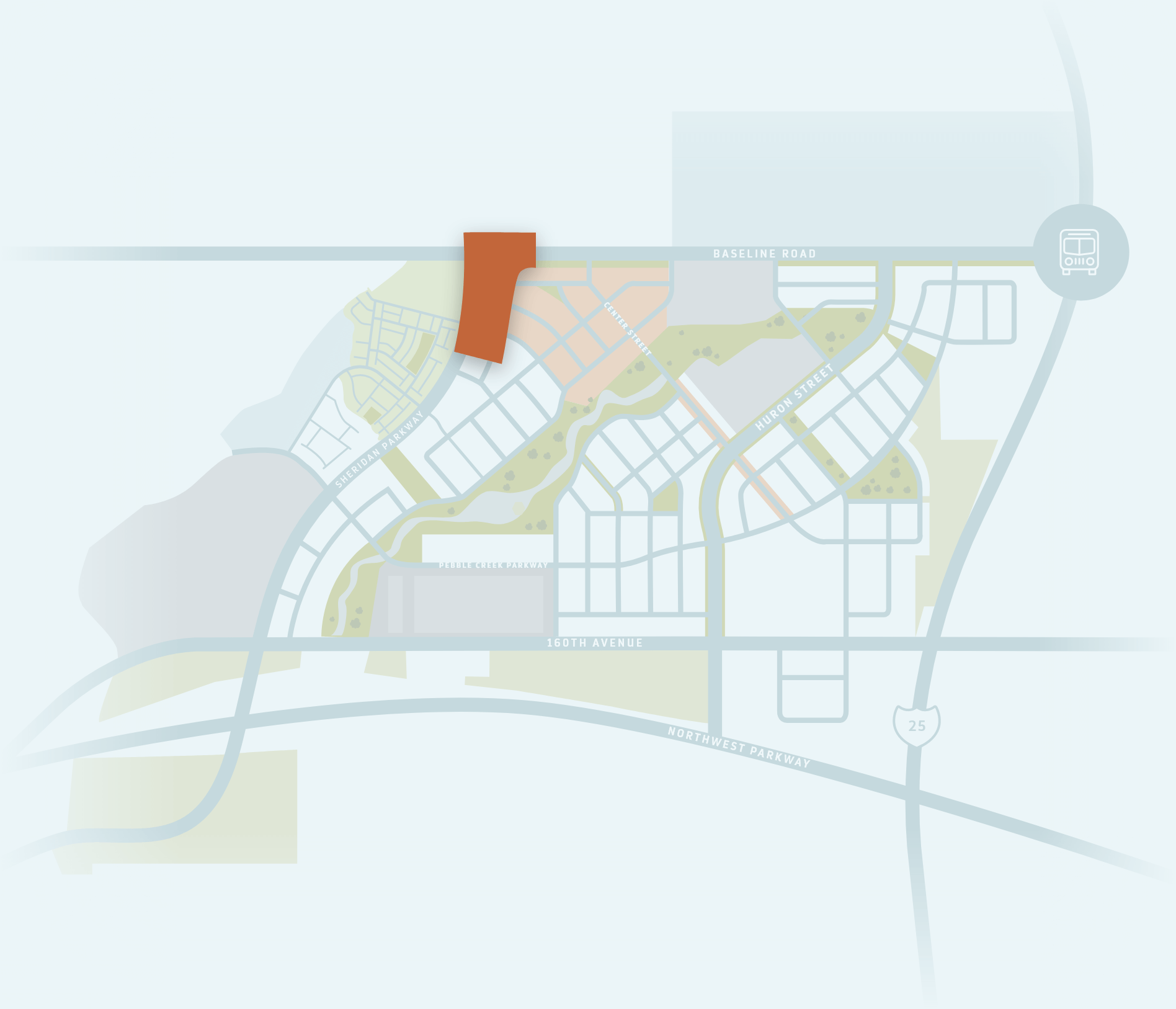
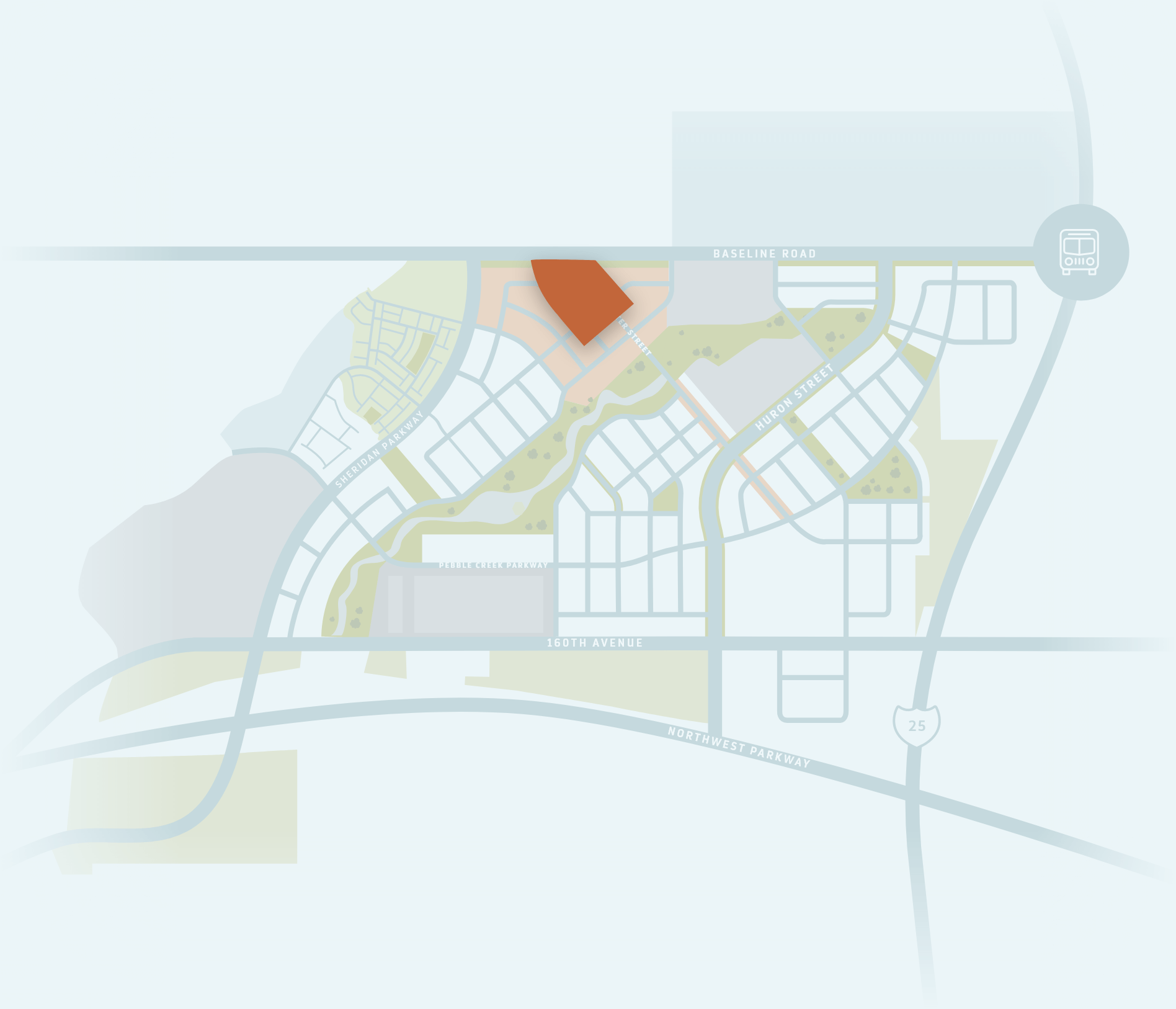
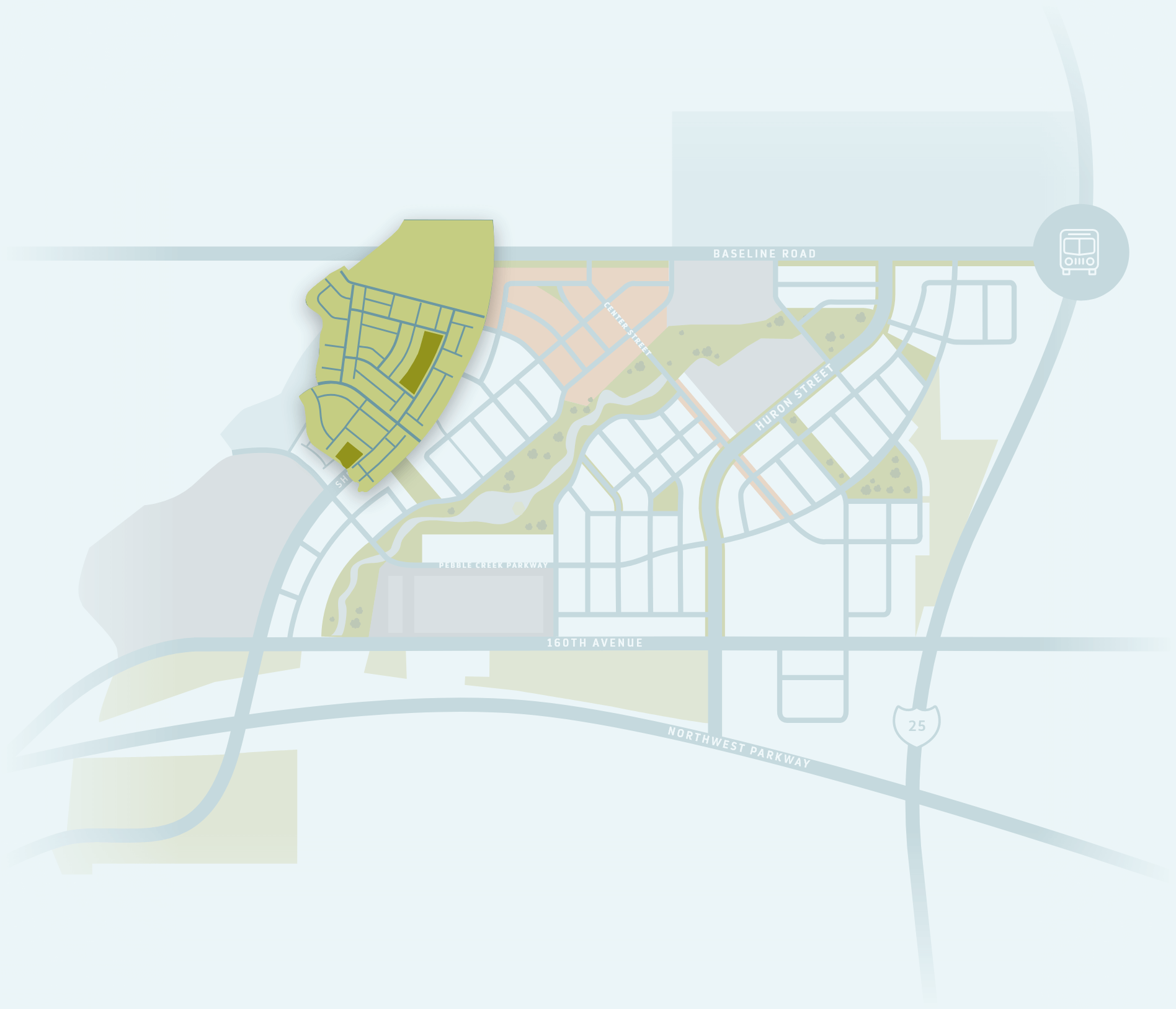
The map produced by Pen Test Partners exploited apps that demonstrate a user’s location being a distance “away” from whoever is viewing their profile.
If somebody on Grindr programs to be 300 legs away, a group having a 300-foot radius may be drawn round the individual looking at that person’s profile, because they are within 300 foot of the location in just about any feasible way.
But by getting around the place of this individual, drawing radius-specific sectors to complement that user’s distance away since it updates, their precise location may be pinpointed with as little as three distance inputs.
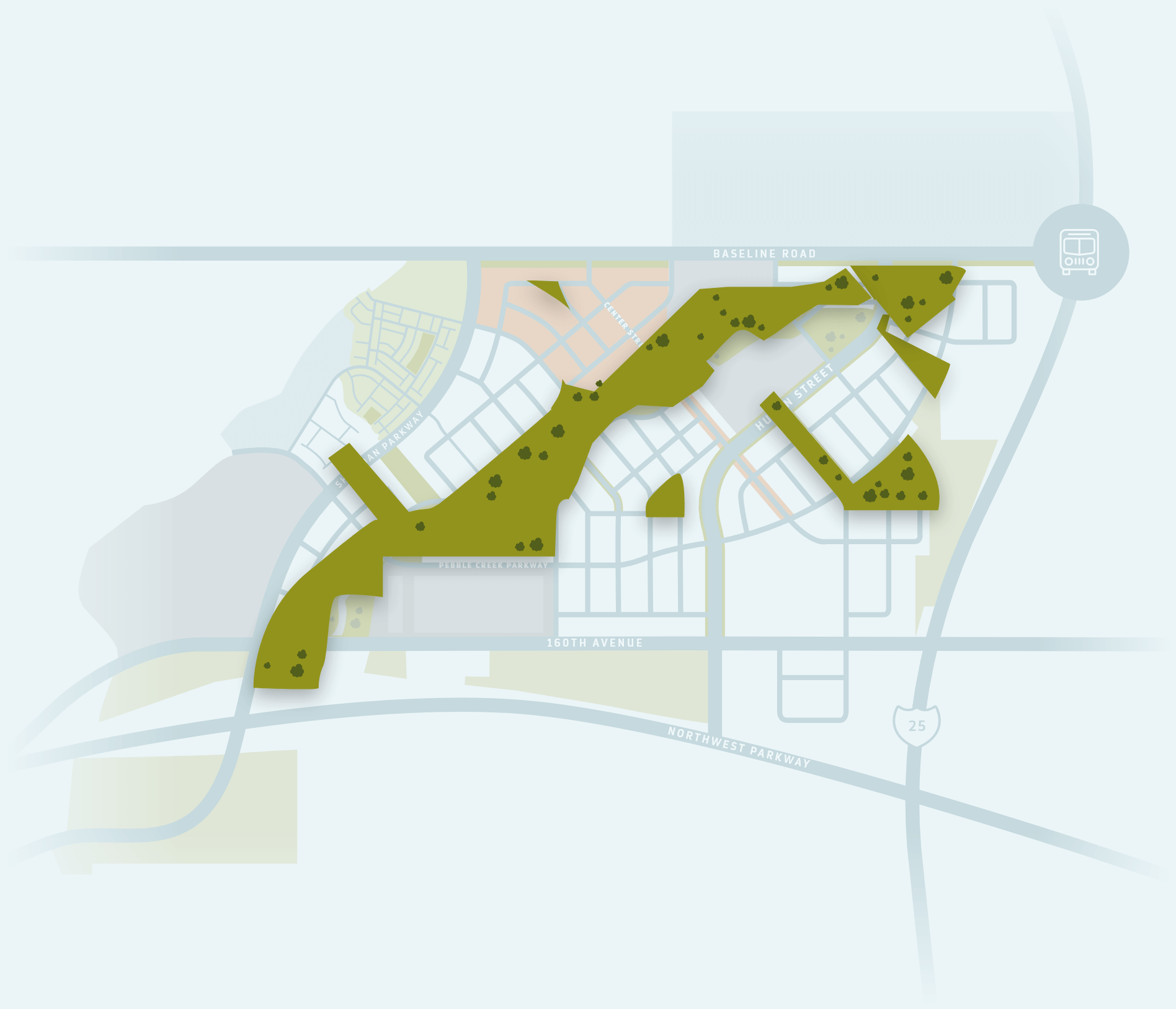
That way — referred to as trilateration — Pen Test Partners researchers produced an automatic tool that could fake a unique location, producing the exact distance information and drawing electronic bands round the users it encountered.
In addition they exploited application development interfaces (APIs) — a core element of computer software development — employed by Grindr, Recon, and Romeo that have been perhaps not completely guaranteed, allowing them to build maps containing a huge number of users at the same time.
“We believe that it is definitely unsatisfactory for app-makers to leak the location that is precise of clients in this fashion,” the scientists published in an article. “It makes their users in danger from stalkers, exes, crooks and country states.”
They offered a few answers to repair the problem and avoid users’ location from being therefore easily triangulated, including restricting the precise longitude and latitude information of the person’s location, and overlaying a grid for a map and snapping users to gridlines, as opposed to particular location points.
“Protecting specific data and privacy is hugely crucial,” LGBTQ liberties charity Stonewall told BBC Information, “especially for LGBT individuals globally who face discrimination, also persecution, if they’re available about their identification.”
Recon has since made modifications to its software to cover up a user’s precise location, telling BBC Information that though users had formerly valued “having accurate information when searching for users nearby,” they now understand “that the danger to your users’ privacy connected with accurate distance calculations is simply too high and now have consequently implemented the snap-to-grid solution to protect the privacy of your users’ location information.”
Grindr stated that user’s curently have the possibility to “hide their distance information from their pages,” and added so it hides location information “in nations where its dangerous or unlawful to be a part associated with LGBTQ+ community.”
But BBC Information noted that, despite Grindr’s declaration, locating the precise areas of users within the UK — and, presumably, far away where Grindr doesn’t conceal location information, such as the U.S. — was still feasible.
Romeo stated it will take protection “extremely really” and enables users to correct their location to a place regarding the map to cover their location that is exact this is certainly disabled by default as well as the company apparently offered hardly any other recommendations about what it might do in order to avoid trilateration in future.
In statements to BBC Information, both Scruff and Hornet stated they currently took actions to hide user’s precise location, with Scruff employing a scrambling algorithm — though it offers become switched on in settings — and Hornet using the grid technique suggested by researchers, in addition to allowing distance to be concealed.
For Grindr, this will be still another addition to your ongoing business’s privacy woes. Just last year, Grindr ended up being discovered become sharing users’ HIV status along with other businesses.
Grindr admitted to sharing users’ two outside companies to HIV status for testing purposes, along with the “last tested date” if you are HIV-negative or on pre-exposure prophylaxis (PrEP).
Grindr stated that both companies had been under “strict contractual terms” to give you “the greatest degree of privacy.”
Nevertheless the information being provided ended up being so— that is detailed users’ GPS information, phone ID, and e-mail — so it could possibly be utilized to recognize certain users and their HIV status.
Another understanding of Grindr’s information protection policies arrived in 2017 whenever a D.C.-based designer created a internet site that allowed users to see that has formerly obstructed them from the software — information which are inaccessible.
The web site, C*ckBlocked, tapped into Grindr’s very own APIs to produce the info after designer Trever Faden unearthed that Grindr retained record of whom a person had both obstructed and been blocked by within the code that is app’s.
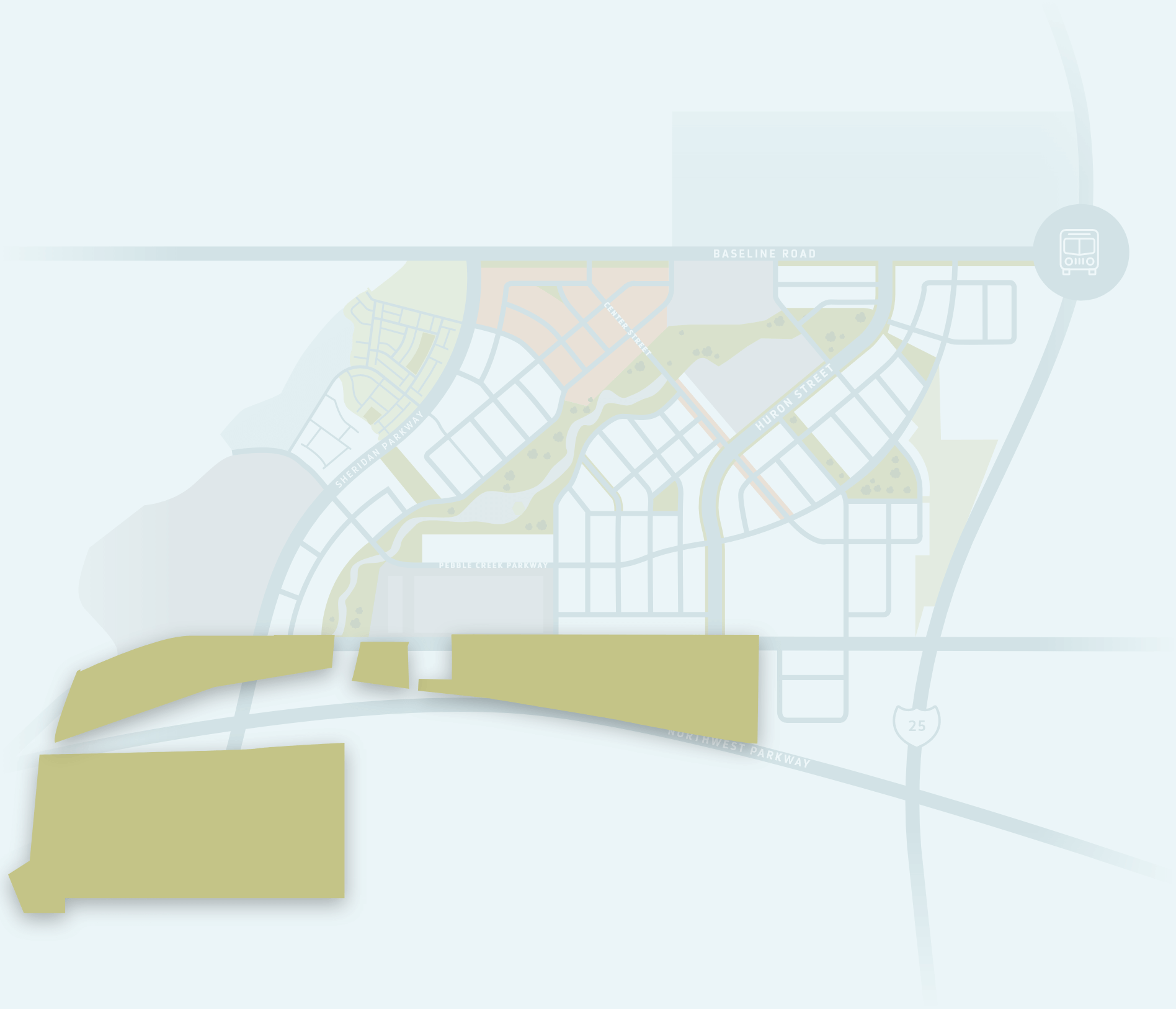
Faden additionally unveiled he can use Grindr’s information to come up with a map showing the break down of specific pages by community, including information such as for instance age, intimate place choice, and basic location of users for the reason that area.
Grindr’s location information is therefore specific that the application is currently considered a nationwide threat to security by the U.S. federal government.
Early in the day in 2010, the Committee on Foreign Investment in america (CFIUS) told Grindr’s Chinese owners that their ownership for the app that is dating a danger to nationwide safety — with conjecture rife that the clear presence of U.S. military and intelligence workers regarding the software would be to blame.
That’s to some extent due to the fact U.S. federal government is now increasingly thinking about exactly how app designers handle their users’ private information, specially personal or painful and sensitive information — like the location of U.S. troops or a cleverness official utilizing the software.
Beijing Kunlun Tech Co Ltd, Grindr’s owner, has got to offer the software by June 2020, after just using total control over it in 2018.